Understanding the NIGHT-DUST model
Token volatility and unpredictable gas costs have made blockchain infrastructure commercially unworkable for most institutions and businesses.
The NIGHT-DUST token-resource model mitigates that problem, and is a critical and novel feature of the Midnight network.
Most blockchain architectures face a persistent challenge: balancing network security with operational predictability. In traditional models, users pay transaction fees using the network's native token, which is also a capital asset. When the market price of that asset rises, transaction costs become prohibitively expensive, creating a barrier to entry for new users and businesses, and a disincentive for existing ones, as holding an appreciating asset becomes more attractive.
Midnight decouples the network resource from the capital asset and ensures predictable operational costs through two distinct components:
- NIGHT: The native utility token used for generating DUST. It functions as a capital asset and a store of value. It is also designed to be used for governance, staking, and securing the network.
- DUST: A non-transferable, renewable resource used exclusively to pay for transaction fees.
Holding NIGHT automatically generates DUST over time. Read the latest blog to learn more about the mechanics of DUST generation and decay.
For developers, learn more about the process of generating DUST from NIGHT, including practical tips for planning transactions and costs, in this explainer video:
Community Research Results
The Midnight network is defined, shaped and strengthened by the whole community. In late 2025, the Midnight Foundation opened its second annual community survey to gather direct feedback from this expanding global community. Throughout 2026, the Foundation has shared insights from these results to ensure the network evolves alongside the needs of its builders, transforming community data into functional, privacy-first features.
Recent publications highlight the rapidly expanding growth of the Midnight community around the world, and how attitudes to privacy serve as a unifier across different communities and ecosystems.
The latest results from the community research build on previous findings and identify a critical gap between privacy requirements and user experience. The Midnight community is optimistic and excited about privacy features. To build successful DApps, developers must prioritize intuitive design that makes privacy outcomes effortless for the end user.
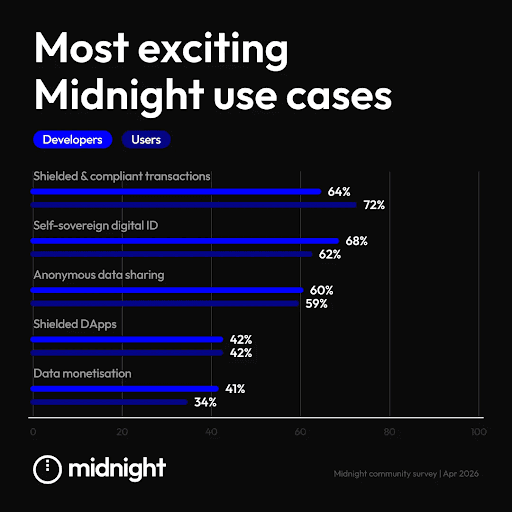
Key insights
- Privacy as a foundation for utility: Interest in data monetization is dependent on robust privacy protections.
- Sector-specific UX requirements: The survey identifies users of certain categories of DApp that may have less experience and lower tolerance for technical friction.
- Alignment on growth areas: Both developers and users believe decentralized finance (DeFi) and real-world assets (RWAs) are the sectors with the highest growth potential.
Learn more in the latest community survey results blog.
Applications
Midnight.fun
The catalog of games, applications and demos on midnight.fun is now live, featuring the first three games that demonstrate programmable privacy and ZK technology. These games are live on the network and are open-source templates and functional examples of Midnight in action.

Four games are currently available, with more coming soon:
- Dust 2 Dust: Progress through dungeon battles by assembling strategic teams. Dust 2 Dust demonstrates how to handle the depth of a traditional database without exposing personal activity. It secures on-chain randomness via iterative hashes, ensuring outcomes are fair, unpredictable, and fully verifiable by the network.
- Kachina Kolosseum uses private state functionality to implement a fog of war mechanic. It demonstrates how developers can maintain a shared, verifiable truth and enforce game rules without exposing tactical data on a public ledger.
- Block Kart Legends is a racing game that highlights high-performance execution and cross-chain functionality. It uses a dual-layered approach where an on-chain node calculates scores while the frontend renders the simulation in real-time, ensuring gameplay remains fluid and mathematically consistent with the ledger.
- Safe Solver features on-chain randomness and deterministic mechanics. It serves as a technical blueprint for backend synchronization and verifiable state updates, showing how the protocol handles high-stakes user decisions and immediate session resolution.
Read the full article to explore the technical architecture and protocol functions these games demonstrate.
Network Observation
The Midnight network is now live, and everyone can see the network in action and monitor live network activity
More detailed network metrics are currently being refined for future State of the Network editions; the community can monitor real-time activity, block production, and transaction volume through several block explorers from Midnight partners.
- Midnight Explorer: https://midnightexplorer.com/
- Subscan: https://midnight.subscan.io/
- Webisoft: https://explorer.1am.xyz/
Ecosystem
In addition to hackathons, several new programs now offer structured pathways for builders to contribute to the network’s expanding library of resources and partner integrations.
Hackathons
Congratulations to the winners of the recent Into the Midnight hackathon, in collaboration with Rise In. Builders pushed the boundaries of ZK technology across five tracks: Identity & Governance, Finance & DeFi, Consumer Applications, Healthcare, and AI. Learn more about the winners and their projects.
The next virtual Midnight hackathon is coming up in May and is open to teams from anywhere in the world. This 48-hour event is the first major hackathon since the launch of the network, offering builders the chance to create production-ready DApps on the network and solve the world’s biggest privacy challenges. The hackathon starts May 15, 2026, at 13:30 UTC. Visit the hackathons page to register and learn more.
More hackathons are coming up, so keep an eye on the blog to learn about winning projects, and check the hackathons page to see what’s next.
Eclipse Content Bounty Program
The Midnight Foundation has launched Eclipse, the next phase of the Content Bounty Program. Building on insights from the pilot round, Eclipse focuses on high-quality, original technical content that supports developers in building on the network. The program incentivizes the creation of written tutorials, video walkthroughs, and code examples that simplify the onboarding process for the Midnight architecture.
Learn how to participate in Eclipse.
Partner Sprint Zealy Quests
A new series of Partner Sprints has launched to drive hands-on engagement with tools shipping in the Midnight ecosystem. These two-week cycles guide developers through the integration of partner SDKs and services using structured technical quests.
The program focuses on momentum and real-world usage, rewarding top contributors who build and submit projects using live ecosystem tooling. These sprints provide a direct feedback loop between developers and partners, ensuring that new products reaching mainnet are robust, well-documented, and ready for integration.
Releases & Documentation
Updates occur regularly. Check the releases page and the compatibility matrix frequently.
Midnight.js 4.0.4 introduces the @midnight-ntwrk/midnight-js barrel package and the addition of @midnight-ntwrk/midnight-js-dapp-connector-proof-provider along with further updates. Review the release notes for a complete list of changes and updates.
Join the conversation
There’s more to learn every week on the Developer Fireside Hang. Pull up a seat and join the conversation every Wednesday at 15:00 UTC on YouTube.
To talk with the community about everything Midnight, join the community on Discord.